Over the past eleven weeks, we outlined a range of recommendations that, if implemented, will prevent up to 85 per cent of all breaches. Many in the technology industry deem fixing human error the most crucial step any organisation can take in this fight.
How most breaches used to happen
Modern information security breaches follow a specific pattern, and most organisations are not fully equipped to stop these attacks. Hackers compromise firewalls, subvert intrusion detection systems and a host of other edge-based/perimeter-based security layers: all this required vulnerability detection, exploitation and a host of skills and tools to accomplish. Similarly to military tactics and weapons to advance, so too do the methods of cyber threats. With these advancements, cyber attackers have come up with multiple ways to bypass edge protection and gain direct access from inside the network.
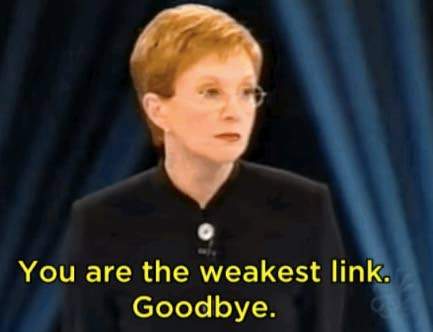
You, the user, are now the weakest link. Hackers figured out how to get you to install some form of malicious software (malware) through e-mail phishing, to unknowingly enter an incorrect site, allowing your kids to play games on unsecured websites and more. In other words — get YOU, the user, to create a back door to your system. As sophistication increases, many organisations fail to detect breaches for months and sometimes years later.
Cybersecurity Awareness
IT security professionals consider Security Awareness Training as the most effective protection from ransomware. Because the criminals are continually trying to make employees click on malicious links or open up infected attachments, an essential part of the training is showing users what these phishing e-mails and what these links look like.
We have found that the three-step Security Awareness Training programmes to be the most effective.
Step 1. Baseline Test – with the support and explicit approval from the organisation’s leadership, launch a simulation to establish the “phish-prone” percentage level.
Step 2- Conduct the awareness training for the entire company and then Step 3 – Again, with the approval from the organisation’s leadership, launch another more significant simulated phishing attack on all the users in the organisation.
One major vendor’s survey showed that the overall industry initial phish-prone percentage benchmark turned out to be a troubling 31.4 per cent. Fortunately, the data showed that this 30 per cent could be brought down by nearly half to just 16.4 per cent in only 90 days by deploying security awareness training. The 365-day results show that the final phish-prone percentage can be minimised to 4.8 per cent on average by following these best practices. It pays to be aware, very aware.
Christopher Reckord is CEO of managed IT services provider tTech Limited. Trevor Forrest is the founder and CEO of 876 Technology Solutions. Collectively, they have approximately 80 years of experience helping organisations of varying sizes procure and implement information technology solutions and transform digitally.
Click here to view original web page at www.jamaicaobserver.com